- TypeScript
- React
- NodeJS
- MongoDB
- GraphQL
Nice to meet you!
I'm Jamel Hammoud, a Full Stack Software Engineer at Envoy, an SF-based tech company. Envoy's mission is to build the workplace of the future.
As an engineer on the Spaces Team, I empower workplace administrators around the world to efficiently manage their buildings & employees.

Go ahead, do it!
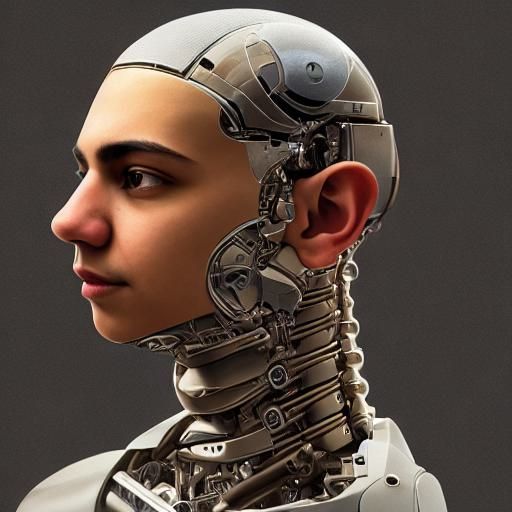
Using Dreambooth (Stable Diffusion) to generate images of myself.We are living in the future. Leveraging the power of open-source Stable Diffusion, I trained an AI model to generate images of me based on a text prompt.
Building an OAuth Flow for Circle.so’s Custom SSO.Custom single sign-on isn't easy. Here's an overview of how I did it for Social Curator's Circle.so-powered community.
Fooling around with OpenAI's Dall•E image generation.Using OpenAI's DALL•E to generate images from unique text prompts.
- PLAY HOMIE
Homie
A fun little web-based game where you guess the sale-value of a home by going through its 3D virtual tour.
- SEE LANDING PAGE
Crosswalk
Your gateway into the unseen world around you. Drop & discover hidden messages wherever you find yourself.
- SEE REDDIT POST
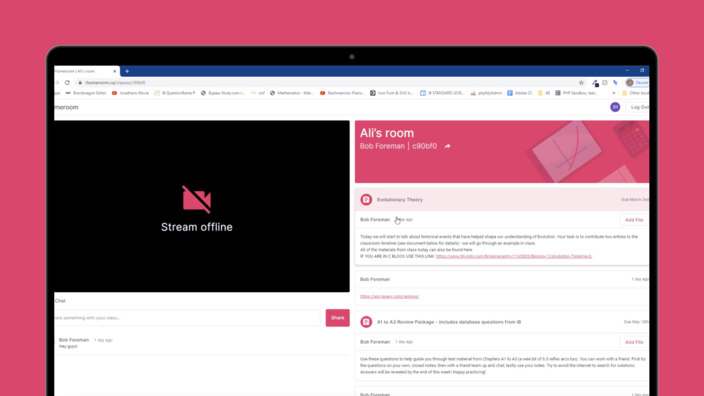
iHomeroom
A small online platform to help my teachers stay connected with us during our school closure.
- SEE CODE ON GITHUB
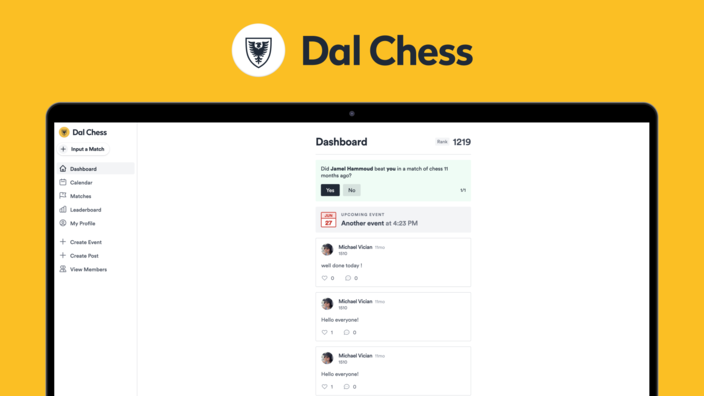
DalChess
A web application for the Dalhousie Chess Club to keep up-to-date on club events, record your matches and see your auto-generated scores.
- SEE CODE ON GITHUB
React Boiler
A template repository containing all the boiler code I need when building React + Typescript projects.
Jmoji
A Discord bot that brings my favorite part of Snapchat (Bitmojis) to Discord.
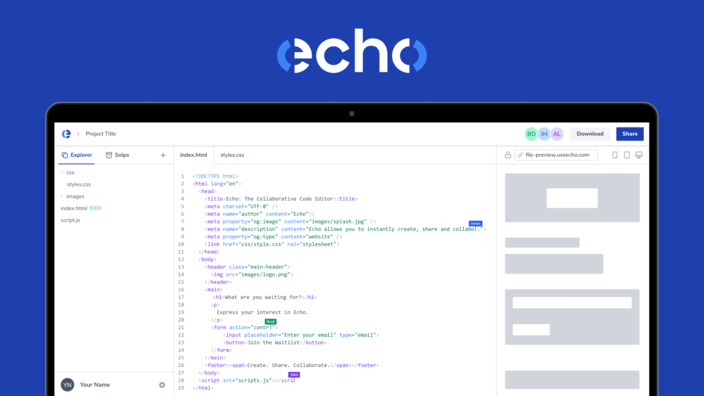
Echo
A web-based workspace that allows you to instantly create, share and collaborate on code.